Top Hacker Forums in 2026: A Cybersecurity Researcher’s Guide
 2026.01.19 12:10
2026.01.19 12:10Why Hacker Forums Matter for Cybersecurity in 2026
If you’ve worked in cybersecurity for a while, you start to notice something a bit unsettling.
The earliest hints of what’s coming next often appear in the hidden corners of the internet—before they hit your SIEM alerts, before vendors release a CVE writeup, and long before a polished blog post pops up on LinkedIn.
That’s why keeping an eye on hacker forums matters. Not to play the role of an attacker or for casual curiosity—but because these forums are where techniques are tested publicly, tools are shared, criminals recruit, reputations are made, and the first signs of a new wave of exploitation often surface.
This article is strictly about education, defense, and threat intelligence. It focuses on understanding attacker behavior, identifying early phishing and malware trends, tracking access broker activity, and recognizing how cybercrime ecosystems actually function. It is not a how-to hacking guide, and it is not about buying or using illegal services.
One important note from the start: monitoring hacker forums can put your privacy and organization at risk. Many communities are hostile to outsiders, actively track users, or distribute malware. This is why professional threat intelligence teams rely on isolated research environments and specialized browsing tools, rather than standard consumer browsers.
What Are Hacker Forums? (And Why the Term Is Misleading)
A hacker forum is basically any online community where people talk about hacking-related topics. This can range from legitimate, moderated spaces where security professionals share research, to riskier corners where stolen access is traded and members argue over whose malware or stealer logs are “freshest.”
The term “hacker” can mean a lot of different things. In practice, most forums tend to fall into a few clear categories, depending on their focus and user base.
1. Ethical, legal communities (Low Risk)
These are places where people discuss:
· Vulnerability research and exploitation concepts (often responsibly)
· Reverse engineering and malware analysis
· Bug bounty strategy and writeups
· Defensive tooling, detection engineering, and OPSEC
· CTFs and learning resources
They might still contain sharp technical content, but the intent is education and improvement. They tend to have moderation, public visibility, and some kind of norms.
2. Grey-Zone Forums (Mixed Intent, Higher Risk)
Some forums fall into a grey zone. They might be labeled as “research-focused,” but still allow content that’s questionable—or host discussions that can be used for both attack and defense. You’ll see debates like, “Is sharing a PoC harmful?” The usual answer: it depends—and the internet rarely agrees.
These spaces are important because they’re often where new techniques get dissected and tested quickly. At the same time, they carry higher risks, both technically and legally. Always be aware of your organization’s policies and the laws in your jurisdiction before engaging with—or even observing—these forums.
3. Illegal Underground Hacker Forums and Marketplaces (High Risk)
Some underground forums and marketplaces exist purely for criminal activity. They are commonly used to:
· Sell stolen credentials, cookies, tokens, and stealer logs
· Trade initial access, such as RDP, VPN, or cloud accounts
· Sell exploits, malware, or ransomware-as-a-service
· Recruit affiliates, money mules, or other “support” roles
· Coordinate targeting by industry or geographic region
From a defender’s perspective, these spaces matter because they are directly embedded in the attack lifecycle. This isn’t theoretical or academic—it’s where real operations are planned, supplied, and scaled.
The challenge is that interacting with these forums can cross legal boundaries very quickly. Even passive monitoring carries risk if it’s done without proper safeguards, legal guidance, and strict operational discipline.
How Hacker Forums Impact Real-World Cybersecurity
Hacker forums influence cybersecurity risk in several direct ways.
· Faster Exploitation Cycles: Once a vulnerability is made public, forums and chat groups often turn it into working attack techniques within hours.
· Industrialization of Crime: You will see things like customer support for phishing kits, SLAs for botnets, and even refund policies. Cybercrime has become a business.
· Access Brokering and Specialization: One group steals credentials, another sells access, and another deploys ransomware. Forums connect all the pieces.
· Leak Propagation: A data dump might appear in one place, get mirrored elsewhere, and eventually become searchable. Monitoring these forums can give defenders an early warning.
· Reputation Economies: Vendors and actors build credibility on forums. Tracking who is trusted can help with threat attribution and prioritization.
Hacker forums matter. The tricky part is monitoring them safely without turning your threat intelligence program into a legal or operational liability.
Top 10 Underground and Gray-Area Hacker Forums (High Risk Examples)
The following communities are mentioned strictly for cybersecurity education and threat intelligence research. They illustrate how hacker forums function but should not be accessed casually or without proper safeguards.
1. Hack Forums
One of the earliest English-language hacker communities. Historically mixed beginner hacking discussions, social engineering, and low-level cybercrime. Today it is often referenced as an entry-level forum rather than a high-value intelligence source.
2. Exploit.in
A long-running Russian-language underground forum focused on exploits, malware development, and access trading. Frequently cited in professional threat intelligence reports due to its role in connecting exploit developers and access brokers.
3. Leakbase
A marketplace-oriented forum associated with leaked databases, credential dumps, and breach data. From a defensive perspective, it helps illustrate how stolen data is packaged, priced, and redistributed.
4. XSS.is
A technically advanced Russian-speaking forum known for exploit development, access brokerage, and collaboration between specialized threat actors. Considered one of the more influential top hacker forums in intelligence research.
5. Dread Forum
A discussion-oriented forum historically linked to dark web markets. Functions more like a Reddit-style community for underground discussions, scam warnings, and operational security conversations.
6. Altenen
Previously known for sharing credential “combo lists.” Often referenced in breach analysis as an example of how leaked credentials circulate before reaching larger aggregation platforms.
7. Creaked.io
A hybrid community covering game cheats, cracking tools, and entry-level cybercrime topics. It highlights the blurred line between gray-area experimentation and illegal activity.
8. CraxPro
A smaller forum focused on cracking tools, account abuse techniques, and automation scripts. Educationally useful for understanding how commoditized attack tools are shared.
9. Nulled
A large English-language forum combining cracking tools, leaked resources, and digital service abuse. While not always deeply technical, it demonstrates how cybercrime is productized and scaled for non-expert users.
10. BlackHatWorld
Often misunderstood as a pure hacker forum, BlackHatWorld is better described as a gray-hat digital marketing community. Discussions focus on SEO manipulation, automation, account farming, and growth tactics. From a cybersecurity perspective, it is useful for studying abuse patterns rather than advanced exploitation.
These examples demonstrate why defenders should monitor categories of communities, not depend on a single “top hacker forum” URL.
Most organizations do this through specialized vendors, closed intelligence groups, or dedicated analysts operating under strict legal guidance. If you are a solo researcher or a small team, the safest approach is to consume intelligence reports derived from these sources, rather than engaging directly.
Legal Alternatives for Cybersecurity Research
Most organizations do not monitor underground forums directly. Instead, they rely on legal, high-signal alternatives that surface early indicators without direct exposure.
1. Vulnerability Research and Exploit Signals
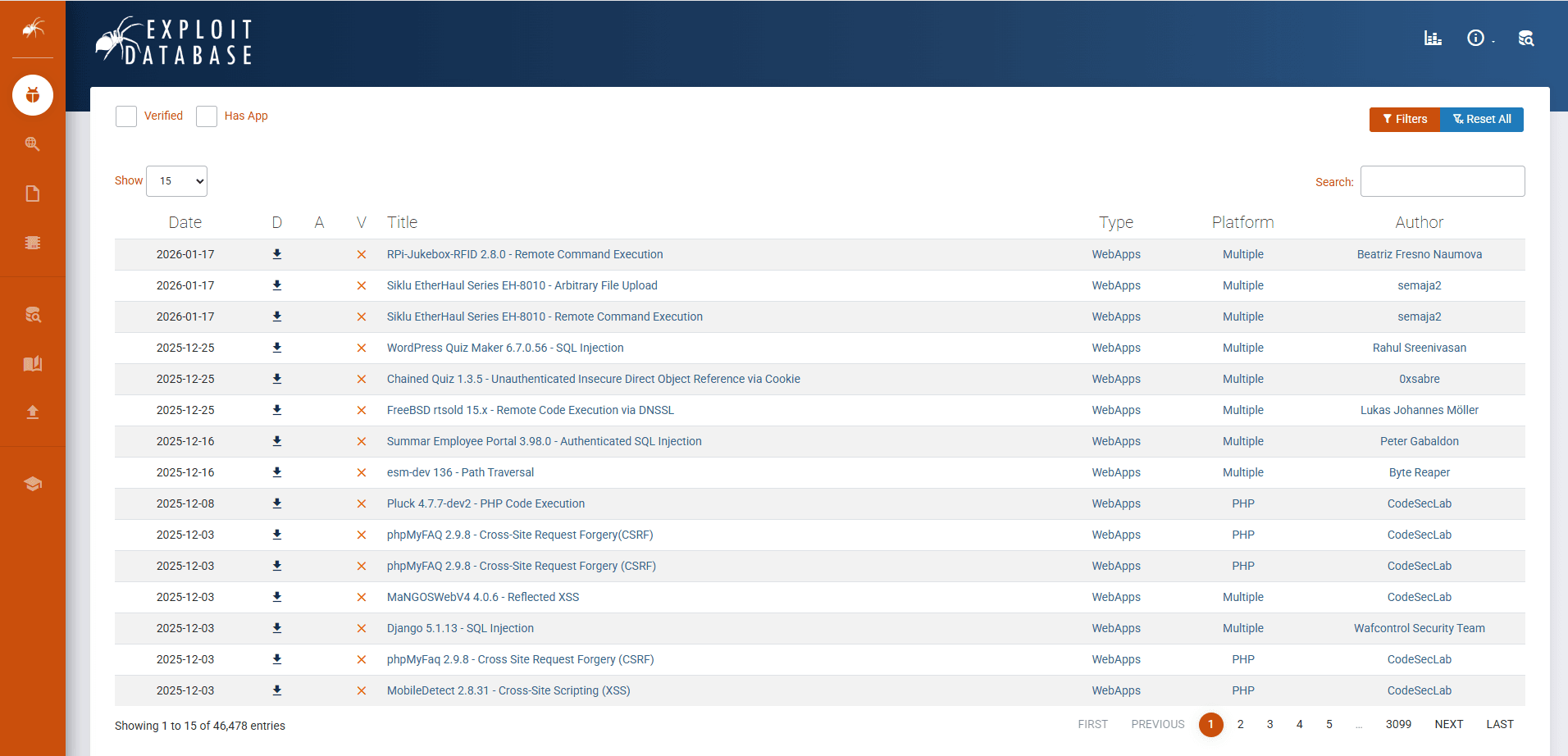
(1) Exploit-DB
Exploit-DB is not a forum in the traditional sense, but it has been a long-running archive of public exploits and proof-of-concepts (PoCs). Monitoring it helps you see when a vulnerability moves from theoretical to weaponizable in the wild. If you combine it with CVE monitoring, you get a clearer picture of exploit maturity.
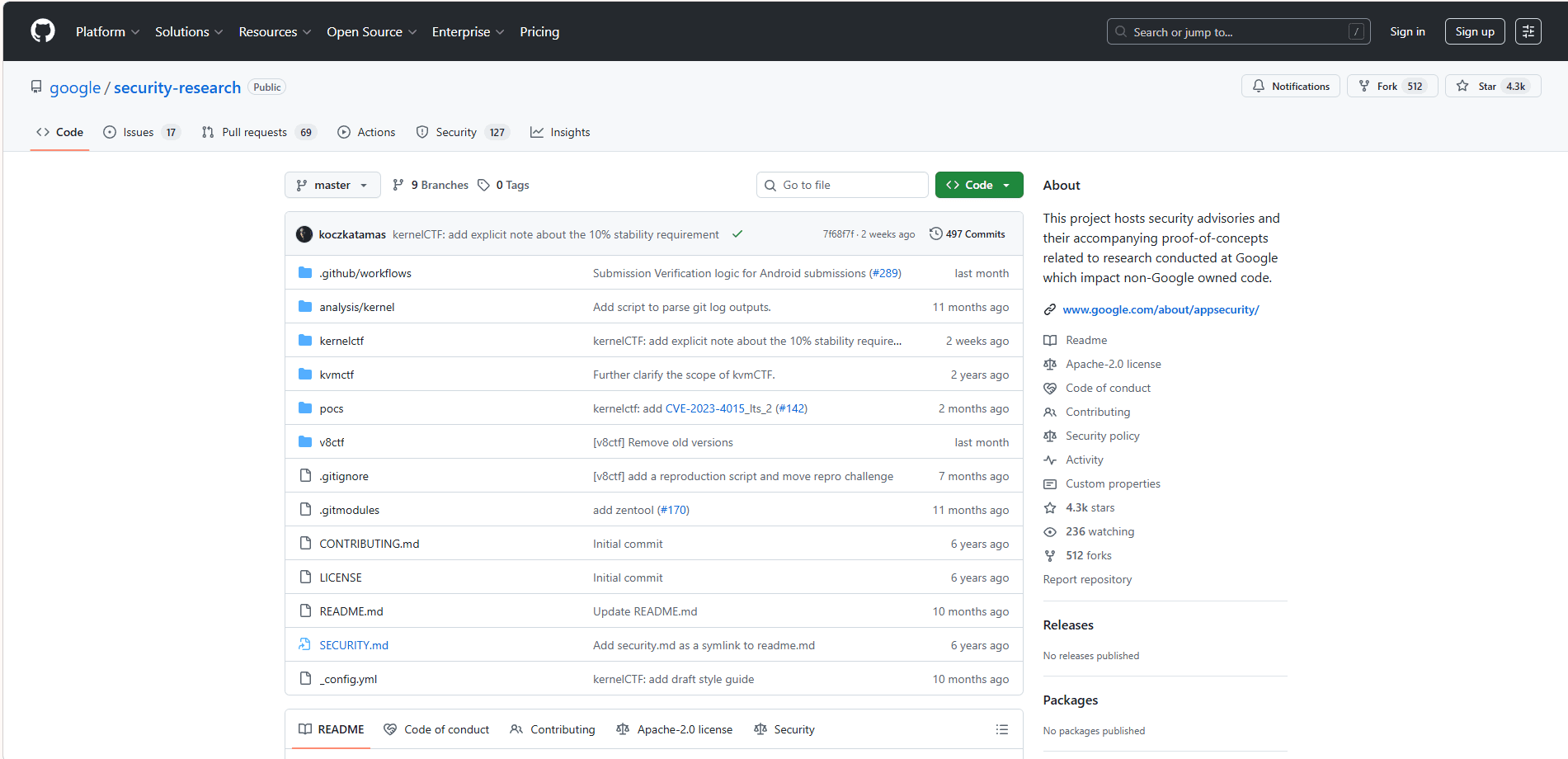
(2) GitHub (Security Research Corners)
GitHub is another platform that is not a forum, yet many exploit PoCs, reverse engineering tools, and detection bypass research are published here first. Monitoring relevant repositories, issues, and forks around major CVEs can give you early indicators that exploitation is about to become widespread.
(3) Google Groups and Security Mailing Lists
Old school, but still valuable. Some of the best technical disclosures appear on mailing lists before they are summarized on social media.
Examples Worth Tracking
· oss-security
· Vendor-specific security advisories and mailing lists
· Research-oriented lists tied to languages and frameworks that are relevant to your environment
Monitoring these sources is about staying ahead of exploitation trends. They provide high-quality signals for defenders and researchers, while being fully legal and safe when used for threat intelligence and defensive work.
2. Ethical Hacking Communities (Good for Tactics, Trends, and Mindset)
(1) Hack The Box (HTB) Forums
HTB is primarily training-focused, but its forums can reveal which techniques are trending, what tools people are learning, and which misconfigurations are most common. For defenders, it provides a subtle way to see what “new attackers” are practicing at scale without engaging in illegal activity.
(2) TryHackMe Community
TryHackMe offers similar value. It is less about underground intelligence and more about understanding the skills pipeline. If you want to know what entry-level threat actors are likely to know in six to twelve months, following popular learning paths is very informative.
(3) Reddit Communities: r/netsec and r/blueteamsec
Reddit can be chaotic, but it is also a fast aggregation layer for write-ups, breach reports, and emerging threats. The comment threads are often the most valuable part, as practitioners call out what is hype versus what is actually being exploited in the wild.
Monitoring these ethical hacking communities allows security teams to stay informed about techniques, mindset, and emerging trends in a fully legal and educational way.
3. Malware Analysis and Reverse Engineering Communities (High Value, Defensive)
(1) Kernelmode.info (Research-Oriented Sections)
Kernelmode.info was a popular forum for malware analysis, reverse engineering, and Windows internals. Researchers often discussed advanced topics like unpacking threats, rootkits, and EDR evasion.
The forum is now closed and archived, so it is no longer active for real‑time discussion. Its historical posts are still valuable for learning, but any research should be done in a strongly isolated environment and follow strict legal and operational guidelines.
Today, security teams rely on active alternatives like GitHub repositories, MalwareBazaar, and other reverse engineering communities to stay up to date.
(2) MalwareBazaar (abuse.ch Ecosystem)
MalwareBazaar is a malware sample repository run by the abuse.ch project. It is not a forum, but it is a critical threat intelligence resource, providing confirmed malware samples for researchers and security teams.
The platform allows access via browsing, API, or feeds, and helps defenders connect underground chatter to real-world malware artifacts, turning discussions into actionable intelligence. Combined with other analysis tools, it provides valuable metadata without needing to execute the malware.
(3) Related Sources in the Same Ecosystem
· URLhaus: Tracks and shares URLs used to distribute malware and phishing campaigns.
· Feodo Tracker: Provides up-to-date information on banking trojans and their command-and-control servers.
· ThreatFox: Collects and shares indicators of compromise (IOCs) for malware campaigns and threat actors.
Monitoring these communities allows defenders to stay ahead of malware trends, understand attacker techniques, and link discussions to actual malicious artifacts, all while maintaining a safe and legal operational posture.
Why a Controlled Browsing Environment Matters When Researching Hacker Forums
Whether you are reading public discussions, tracking leaked indicators, or consuming intelligence reports derived from underground forums, how you access information matters as much as what you read.
Many hacker forums and adjacent communities actively fingerprint visitors, track behavioral signals, and distribute malicious scripts. Even passive observation from a normal browser can expose your real IP, device fingerprint, session data, or organizational identity—creating unnecessary risk for researchers and security teams.
This is why professional threat intelligence workflows typically rely on isolated and controlled browsing environments, rather than standard consumer browsers.
Anti-detect browsers are designed for this exact scenario. They allow researchers to separate identities, isolate sessions, and reduce cross-site tracking by managing browser fingerprints, cookies, storage, and network configurations in a controlled way.
Tools like BitBrowser, an anti-detect browser, are commonly used by security teams and researchers to create isolated environments when monitoring hacker forums for cybersecurity research and security trends.
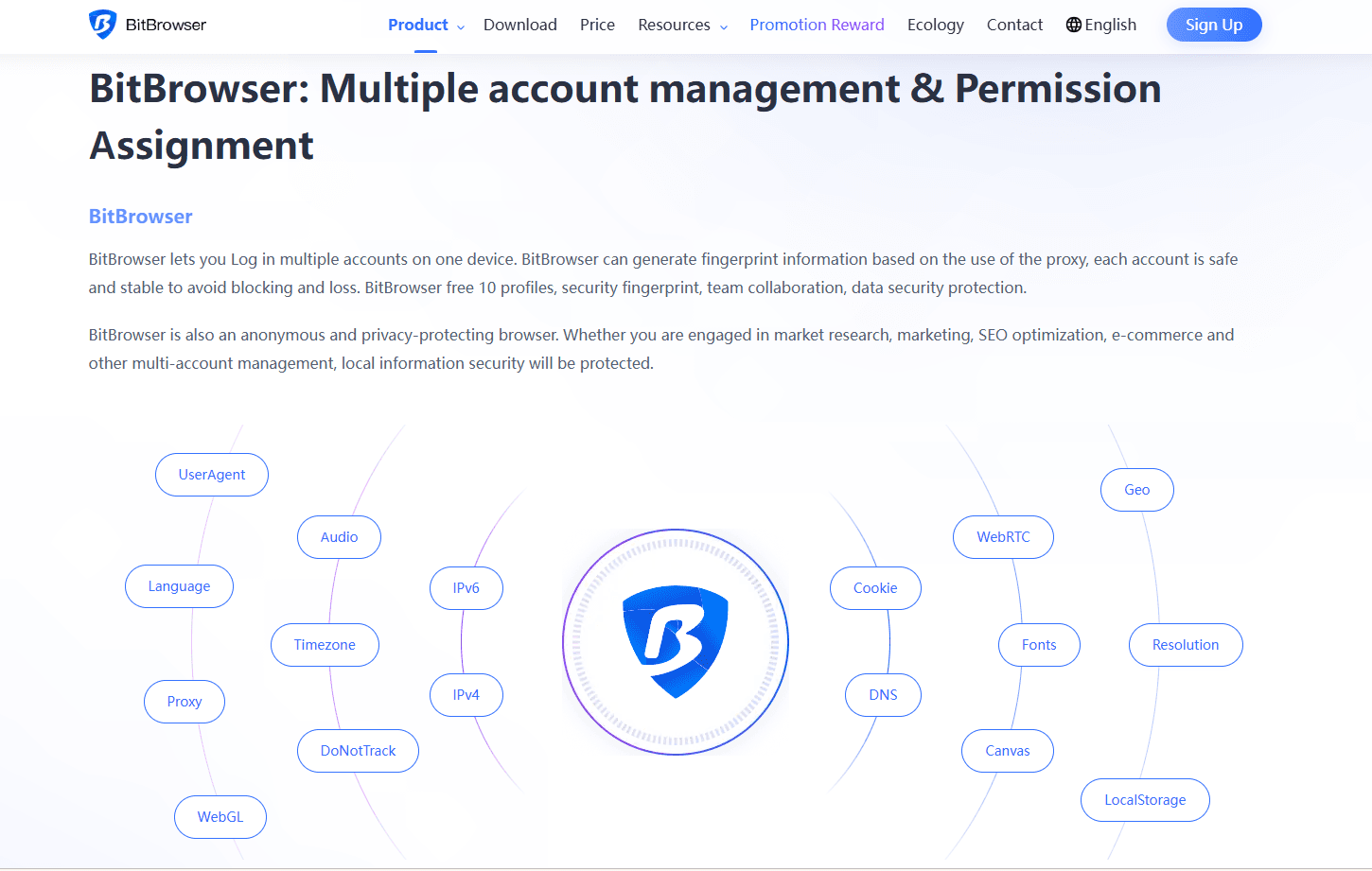
In modern threat intelligence work, a secure browsing environment is no longer optional—it is a basic layer of defense.
Final Thoughts
Hacker forums remain one of the earliest and most reliable signals of emerging cyber threats in 2026. They reveal how exploits are weaponized, how access is traded, and how attacks scale long before traditional security alerts trigger.
At the same time, monitoring top hacker forums comes with real legal, technical, and privacy risks. Effective threat intelligence is not about visiting one famous forum, but about understanding the ecosystem, choosing the right sources, and observing them safely.
For cybersecurity professionals, the goal is simple: learn from hacker communities without becoming exposed to them. With the right workflows, isolation strategies, and tools such as BitBrowser anti-detect browser, researchers can turn high-risk spaces into actionable intelligence—without crossing legal or operational lines.
Frequently Asked Questions (FAQ)
1. Is it legal to browse hacker forums for cybersecurity research?
Reading publicly accessible content for education or threat intelligence is generally legal, but any interaction with illegal content, services, or transactions is not. Laws vary by country, so researchers should always follow internal policies and legal guidance.
2. Why is using a normal browser risky when monitoring hacker forums?
Many hacker forums actively track visitors or distribute malware. Using a regular browser can expose your real identity, device fingerprint, or work environment, which is why security researchers use isolated setups and tools like anti-detect browsers.
3. What is the safest way to learn from hacker forums as a beginner?
Beginners should avoid direct access to underground forums. The safer option is to rely on threat intelligence reports, legal research platforms, and controlled environments, and only consider tools like BitBrowser when operating under clear defensive and educational goals.
 YT.Shi
YT.Shi
 Multi-Account Management
Multi-Account Management Prevent Account Association
Prevent Account Association Multi-Employee Management
Multi-Employee Management